In two recent articles in this website, we discuss Quantum Physics (QP), the remarkable scientific discovery of the 20th century that has revolutionized science as well as all aspects of our civilian and military lives.
The first article [1] discussed several mysteries of QP, notably, particle-wave duality, uncertainty principle, probabilistic interpretation of experiments, act of measurement can change what you are observing, and the superposition principle.
The second article [2] discussed what Einstein called “spooky action at a distance,” experimental verification of QP versus deterministic predictions of local hidden variable theories a la Bell’s Theorem, and quantum entanglement.
The current article discusses how Quantum Physics’ superposition principle and the concept of entanglement can lead to major breakthroughs for computer processing power and computer security.
Brief Review of Computer Bits and Their Physical Implementation:
First we briefly review some of the basics of computers. All information in computers are represented by bits of data. A bit of data can be represented by a 0 or 1, or on or off in terms of an electrical circuit or switch. When we process data in a computer, we are processing a stream of electrical or optical pulses representing 0s and 1s. For example, if we are describing the result of a coin flip, the result is either head (1) or tail (0). So we can represent coin flip with a wire with either electricity or no electricity flowing through it. With transistors, the transistor is turned on when the amount of electricity flowing through the wire connected to the transistor is above a certain threshold, and is turned off when the electricity is less than that threshold. Thus, the coin flip can be described with a single wire connected to a transistor.
What about a more complex situation than describing a coin flip, such as describing which of 3 light bulbs is turned on. Then you need more bits, or more wires, each connected to a transistor, and in this case of 3 light bulbs, you need 3 wires. Thus we see that we can describe more complex physical phenomena by using more and more bits, or more and more wires and transistors.
If we combine 8 bits of data in what is called a byte, which has 28 or 64 combinations. Then a byte can represent the English alphabet. Therefore, information about our world can be represented by combining more bits and bytes together. That is why we hear of terms like kilobytes (a thousand bytes), megabytes (a million bytes), gigabytes (a billion bytes), terabytes (a trillion bytes), petabytes (1,000 terabytes). [3] Bigger and faster computers can simultaneously handle larger and larger number of bytes.
A 200-page book with about 300 words per page has about 60,000 words. A word on the average has about 6 characters. This means that a 200-page book has about 360,000 characters. If we use one byte to represent each character, then this book would have about 360 kilobytes of data.
A newer and better computer usually can process more data and process the data faster than the previous generation of computers. So newer computers will normally have larger or more compact and faster processors and with creative designs in algorithms and software to get additional processing power.
From Bits to Qubits and the Superposition Principle:
With quantum computers, there is a novel way of increasing the processing power and speed without adding more bits which are manifested by adding more circuits and transistors. Instead of using streams of electrical or optical pulses representing 1s or 0s associated with bits, quantum computers use subatomic particles such as electrons or photons and the quantum physics concept of the superposition of states so that a quantum physical system is a superposition of many states. [3] And the system does not collapse to a single state until there is a measurement. The quantum physical system is called a quantum bit or Qubit. So if the quantum physical system is a superposition of n states, then there are n possible 1s or 0s. This means that using a quantum system instead of a traditional system, the number of bits has just been increased by a factor of n.
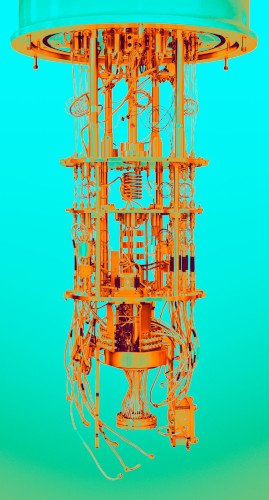
It is not easy to create these quantum physical systems. Generating and managing Qubits is a great scientific and engineering challenge. Currently only a small number of companies and university research labs (such as IBM, Google, Rigetti Computing in Berkeley, and IonQ in College Park) have constructed quantum computers. They use superconducting circuits cooled to temperatures colder than deep space, or trap individual atoms in electromagnetic fields on a silicon chip in ultra-high-vacuum chambers. In both cases, the goal is to isolate the Qubits in a controlled quantum state. To put Qubits into superposition, researchers manipulate them using precision lasers or microwave beams. We are currently at the beginning of the age of quantum computers. That is why most current quantum computers have only a few dozen Qubits, although IBM has announced that they will build a a quantum computer with 1,000 Qubits by 2023. [4]
Partially because of the increase in the number of bits via using Qubits and partially because quantum computers allow novel ways of doing calculations such as simultaneously performing a large number of calculations, quantum computers have the potential of doing calculations that can never be done, or cannot be done in any reasonable amount of time, by traditional computers.
China is also a major player in quantum computers, both in building quantum computers [5] and also in its applications. [6]
Quantum Entanglement and Implications for Cryptography:
In our second article [2] in this series of three article on Quantum Physics, we discuss the hard-to-imagine property of quantum entanglement. This means that a measurement on the state of one particle in a quantum system of two related particles will determine the state of the other particle even if the two particles are now separated in space by a very large distance. This is the QP property that Einstein called “spooky action at a distance,” and is one of the reasons why Einstein and many other physicists did not believe and preferred deterministic theories like “Local Hidden Variable Theories” over a probabilitic theory like Quantum Theory. However, experiments performed during the last 50 years related to Bell’s Theorem have repeatedly verified the predictions of Quantum Theory and ruled out the predictions of “Local Hidden Variable Theories.”
This quantum entanglement property can be beautifully applied to cryptography, which is the practice and study of techniques for secure communication in the presence of third parties called adversaries.
Key to cryptography is to assure that (1) only the intended recipient of any exchange of information can receive the information or can decipher the information, and (2) the information received has not been altered in any way by an adversary. To accomplish (1), we rely on security keys which only the sender and recipient know, or it is too complicated for any adversary to figure out the security key in any reasonable amount of time. To accomplish (2), we need to be alerted if there has been an intrusion.
Quantum computers can help to achieve both (1) and (2). For (1), because of the processing speed of quantum computers, security keys currently used may not be secured enough, i.e., quantum computers can break these security keys. So the expectation of forthcoming larger and larger quantum computers is moving us to use more complex security keys. [7] Furthermore, quantum computers may also offer novel encryption methods. For (2), the entanglement feature of quantum computers will be able to detect that there has been an intrusion, because any action of the intruder will perturb the system and change the state of the system even if one part of the system may be far away from the place of intrusion. [8]
Summary:
In its almost 100 years of existence, quantum physics has completely revolutionized the world and our lives. It has given us many wonderful products that we use everyday, including computers and our daily gadgets such as cell phones, television, GPS. However, we are beginning to enter another revolution brought on by quantum physics when we utilize the superposition principle and quantum entanglement in the construction of our computers. Both the superposition principle and entanglement are fundamental consequences of the probabilistic nature of quantum physics.
[1] “Wonders and Mysteries of Quantum Physics”: http://www.dontow.com/2020/09/wonders-and-mysteries-of-quantum-physics/.
[2] “Paradoxes of Quantum Physics, Bell’s Theorem, What Do Experiments Tell Us?”: http://www.dontow.com/2020/12/paradoxes-of-quantum-physics-bells-theorem-and-experimental-confirmation/.
[3] I found the article “Explainer: What is a quantum computer?” by Martin Giles, in the January 29, 2019 issue of MIT Technology Review an excellent short article summarizing quantum computers: https://www.technologyreview.com/2019/01/29/66141/what-is-quantum-computing/.
[4] “IBM promises 1000-qubit quantum computer—a milestone—by 2023” by Adrian Cho, in Science, September 15, 2020: https://www.sciencemag.org/news/2020/09/ibm-promises-1000-qubit-quantum-computer-milestone-2023.
[5] “China Claims Fastest Quantum Computer in the World,” by Rafi Letzter, LifeScience, December 7, 2020: https://www.livescience.com/china-quantum-supremacy.html.
[6] See, e.g., the article “China Stakes Its Claim to Quantum Supremacy,” by Tom Simonite, Business, December 3, 2020: https://www.wired.com/story/china-stakes-claim-quantum-supremacy/, and the article “Physicists in China challenge Google’s ‘quantum advantage’,” by Philip Ball, Nature, December 3, 2020: https://www.nature.com/articles/d41586-020-03434-7.
[7] For example, the commonly used 2,048-bit RSA system or even the more difficult 4,096-bit key will need to be replaced by even more complex cryotographic systems. See, e.g., “Is Quantum Computing a Cybersecurity Threat?,” by Dorothy E. Denning, March-April 2019, American Scientist: https://www.americanscientist.org/article/is-quantum-computing-a-cybersecurity-threat.
[8] The implementation of quantum entanglement in a communication system was first demonstrated in 2020 by a Chinese team led by Jian-Wei Pan of the University of Science and Technology of China when they simultaneously transmitted a pair of secret keys between two ground stations (located 1,120 kilometers apart) in China via the Chinese satellite Micius. See, e.g., “China Reaches New Milestone in Space-Based Quantum Communications,” by Karen Kwon, June 25, 2020, Scientific American: https://www.scientificamerican.com/article/china-reaches-new-milestone-in-space-based-quantum-communications/. This research was published in June 15, 2020, in Nature.
